A Critical Study on Group Key Management Protocols and Security Aspects For Non-Networks
DOI:
https://doi.org/10.37385/jaets.v4i2.1947Keywords:
Non-Network, Security Issues, Privacy, Cryptography, Group-Key ManagementAbstract
The rise in internet usage and advanced communication systems has led to an increase in security issues. The need for more robust and flexible secure communication has led to the introduction of mobile non-network multicast communication systems like MANET or VANET. Multicasting is increasingly being used for group-oriented applications such as video conferencing, interactive games, TV over Internet, e-learning, etc. To address the security concerns, this paper highlighted the confidentiality, authentication, and access control for non-network multicast communication systems like MANET or VANET. For this, paper explores the group key management protocols. The paper concluded that centralized and asymmetric group key management protocol (GKMP) is most effective for designing secure, and efficient communication models for non-networks. The key findings of the paper are that in group key management protocols (GKMPs) for multicast communication systems adoption of asymmetric GKMPs provides better security, and reduces computational overhead. Therefore, this paper help to improve the robustness and security of multicast communication systems and meet the growing demands of group-oriented applications over the internet.
Downloads
References
Abdollahi, M., Ashtari, S., Abolhasan, M., Shariati, N., Lipman, J., Jamalipour, A., & Ni, W. (2022). Dynamic Routing Protocol Selection in Multi-Hop Device-to-Device Wireless Networks. IEEE Transactions on Vehicular Technology, 71(8), 8796-8809.
Abusalah, L., Khokhar, A., & Guizani, M. (2008). A survey of secure mobile ad hoc routing protocols. IEEE communications surveys & tutorials, 10(4), 78-93.
Azees, M., & Vijayakumar, P. (2016). CEKD: Computationally efficient key distribution scheme for vehicular ad-hoc networks. Australian Journal of Basic and Applied Sciences, 10(2), 171-175., Available at SSRN: https://ssrn.com/abstract=2791871
Belding-Royer, E. M., & Perkins, C. E. (2003). Evolution and future directions of the ad hoc on-demand distance-vector routing protocol. Ad Hoc Networks, 1(1), 125-150.
Bhoi, S. K., Puthal, D., Khilar, P. M., Rodrigues, J. J., Panda, S. K., & Yang, L. T. (2018). Adaptive routing protocol for urban vehicular networks to support sellers and buyers on wheels. Computer Networks, 142, 168-178.
Bilal, M., & Kang, S. G. (2017). A secure key agreement protocol for dynamic group. Cluster Computing, 20, 2779-2792. https://doi.org/10.1007/s10586-017-0853-0
Bondada, P., Samanta, D., Kaur, M., & Lee, H. N. (2022). Data security-based routing in MANETs using key management mechanism. Applied Sciences, 12(3), 1041.
Chen, S., & Wu, M. (2011). Anonymous multipath routing protocol based on secret sharing in mobile ad hoc networks. Journal of Systems Engineering and Electronics, 22(3), 519-527. https://doi.org/10.3969/j.issn.1004-4132.2011.03.023.
Choi, H. H., & Lee, J. R. (2019). Local flooding-based on-demand routing protocol for mobile ad hoc networks. IEEE Access, 7, 85937-85948.
Cui, J., Wei, L., Zhang, J., Xu, Y., & Zhong, H. (2018). An efficient message-authentication scheme based on edge computing for vehicular ad hoc networks. IEEE Transactions on Intelligent Transportation Systems, 20(5), 1621-1632.
Dacosta, I., Chakradeo, S., Ahamad, M., & Traynor, P. (2012). One-time cookies: Preventing session hijacking attacks with stateless authentication tokens. ACM Transactions on Internet Technology (TOIT), 12(1), 1-24.. https://doi.org/10.1145/2220352.2220353
Devi, V. S., & Hegde, N. P. (2018). Multipath security aware routing protocol for MANET based on trust enhanced cluster mechanism for lossless multimedia data transfer. Wireless Personal Communications, 100, 923-940. https://doi.org/10.1007/s11277-018-5358-5
Dhurandher, S. K., Obaidat, M. S., Verma, K., Gupta, P., & Dhurandher, P. (2010). Faces: friend-based ad hoc routing using challenges to establish security in MANETs systems. IEEE Systems Journal, 5(2), 176-188. https://doi.org/10.1109/JSYST.2010.2095910
El-Bashary, M., Abdelhafez, A., & Anis, W. (2015). A comparative study of group key management in MANET. Int J Eng Res Appl, 5(8), 85-94.
El Defrawy, K., & Tsudik, G. (2011). ALARM: Anonymous location-aided routing in suspicious MANETs. IEEE Transactions on Mobile Computing, 10(9), 1345-1358. https://doi.org/10.1109/TMC.2010.256.
El-Hadidi, M. G., & Azer, M. A. (2021, May). Traffic Analysis for Real Time Applications and its Effect on QoS in MANETs. In 2021 International Mobile, Intelligent, and Ubiquitous Computing Conference (MIUCC) (pp. 155-160). IEEE. https://doi.org/10.1109/MIUCC52538.2021.9447611
Fatemidokht, H., Rafsanjani, M. K., Gupta, B. B., & Hsu, C. H. (2021). Efficient and secure routing protocol based on artificial intelligence algorithms with UAV-assisted for vehicular ad hoc networks in intelligent transportation systems. IEEE Transactions on Intelligent Transportation Systems, 22(7), 4757-4769.
Funderburg, L. E., & Lee, I. Y. (2021). A privacy-preserving key management scheme with support for sybil attack detection in VANETs. Sensors, 21(4), 1063. https://doi.org/10.3390/s21041063
Gomathy, V., Padhy, N., Samanta, D., Sivaram, M., Jain, V., & Amiri, I. S. (2020). Malicious node detection using heterogeneous cluster based secure routing protocol (HCBS) in wireless adhoc sensor networks. Journal of Ambient Intelligence and Humanized Computing, 11, 4995-5001. https://doi.org/10.1007/s12652-020-01797-3.
Hammamouche, A., Omar, M., Djebari, N., & Tari, A. (2018). Lightweight reputation-based approach against simple and cooperative black-hole attacks for MANET. Journal of information security and applications, 43, 12-20. https://doi.org/10.1016/j.jisa.2018.10.004.
Hartenstein, H., & Laberteaux, L. P. (2008). A tutorial survey on vehicular ad hoc networks. IEEE Communications magazine, 46(6), 164-171., https://doi.org/10.1109/MCOM.2008.4539481.
He, W., Huang, Y., Sathyam, R., Nahrstedt, K., & Lee, W. C. (2009). SMOCK: a scalable method of cryptographic key management for mission-critical wireless ad-hoc networks. IEEE Transactions on Information Forensics and Security, 4(1), 140-150.
Hillebrand, F. (2002). GSM and UMTS: The Creation o Global Mobile Communication. 3rd ed., John Wiley & Sons, Ltd.
Hinden, R., & Deering, S. (2006). RFC 4291: IP version 6 addressing architecture, Available online: https://www.rfc-editor.org/rfc/rfc4291.html (accessed on 16 January 2021)
Islam, S. H., Obaidat, M. S., Vijayakumar, P., Abdulhay, E., Li, F., & Reddy, M. K. C. (2018). A robust and efficient password-based conditional privacy preserving authentication and group-key agreement protocol for VANETs. Future Generation Computer Systems, 84, 216-227. https://doi.org/10.1016/j.future.2017.07.002.
Khan, A., Sun, Q. T., Mahmood, Z., & Ghafoor, A. U. (2017). Energy efficient partial permutation encryption on network coded MANETs. Journal of Electrical and Computer Engineering, 2017. https://doi.org/10.1155/2017/4657831
Kousar, R., Alhaisoni, M., Akhtar, S. A., Shah, N., Qamar, A., & Karim, A. (2020). A secure data dissemination in a DHT-based routing paradigm for wireless ad hoc network. Wireless Communications and Mobile Computing, 2020, 1-32. https://doi.org/10.1155/2020/2740654
Kumar, K. V., Jayasankar, T., Eswaramoorthy, V., & Nivedhitha, V. (2020). SDARP: Security based Data Aware Routing Protocol for ad hoc sensor networks. International Journal of Intelligent Networks, 1, 36-42. https://doi.org/10.1016/j.ijin.2020.05.005.
Kumar, V., Kumar, R., & Pandey, S. K. (2020). A computationally efficient centralized group key distribution protocol for secure multicast communications based upon RSA public key cryptosystem. Journal of King Saud University - Computer and Information Sciences, 32(9), 1081–1094. https://doi.org/10.1016/j.jksuci.2017.12.014
Kumar, V., Pandey, S. K., & Kumar, R. (2016). Centralized group key management scheme for secure multicast communication without re-keying. arXiv preprint arXiv:1603.01542.
Lim, K., Tuladhar, K. M., Wang, X., & Liu, W. (2017, October). A scalable and secure key distribution scheme for group signature based authentication in VANET. In 2017 IEEE 8th annual ubiquitous computing, electronics and mobile communication conference (UEMCON) (pp. 478-483). IEEE., https://doi.org/10.1109/UEMCON.2017.8249091.
Luo, X., Chen, Y., Li, M., Luo, Q., Xue, K., Liu, S., & Chen, L. (2019). CREDND: A novel secure neighbor discovery algorithm for wormhole attack. IEEE Access, 7, 18194-18205.
Lv, X., Li, H., & Wang, B. (2012). Group key agreement for secure group communication in dynamic peer systems. Journal of Parallel and Distributed Computing, 72(10), 1195-1200. https://doi.org/10.1016/j.jpdc.2012.06.004.
Maheswari, M., Geetha, S., Kumar, S. S., Karuppiah, M., Samanta, D., & Park, Y. (2021). PEVRM: probabilistic evolution based version recommendation model for mobile applications. IEEE Access, 9, 20819-20827. https://doi.org/10.1109/ACCESS.2021.3053583.
Mansour, A., Malik, K. M., Alkaff, A., & Kanaan, H. (2021). ALMS: Asymmetric lightweight centralized group key management protocol for VANETs. IEEE Transactions on Intelligent Transportation Systems, 22(3), 1663-1678. https://doi.org/10.1109/TITS.2020.3029936
Mejri, M. N., Achir, N., & Hamdi, M. (2016, January). A new group Diffie-Hellman key generation proposal for secure VANET communications. In 2016 13th IEEE annual consumer communications & networking conference (CCNC) (pp. 992-995). IEEE. https://doi.org/10.1109/CCNC.2016.7444925.
Othman, J. B., & Mokdad, L. (2010). Enhancing data security in ad hoc networks based on multipath routing. Journal of parallel and Distributed Computing, 70(3), 309-316.. https://doi.org/10.1016/j.jpdc.2009.02.010
Oubbati, O. S., Chaib, N., Lakas, A., Lorenz, P., & Rachedi, A. (2019). UAV-assisted supporting services connectivity in urban VANETs. IEEE Transactions on Vehicular Technology, 68(4), 3944-3951. https://doi.org/10.1109/TVT.2019.2898477.
Perkins, C. E., & Bhagwat, P. (1994). Highly dynamic destination-sequenced distance-vector routing (DSDV) for mobile computers. ACM SIGCOMM computer communication review, 24(4), 234-244.. https://doi.org/10.1145/190809.190336
Qin, Y., Huang, D., & Li, B. (2013). STARS: A statistical traffic pattern discovery system for MANETs. IEEE Transactions on Dependable and Secure Computing, 11(2), 181-192 https://doi.org/10.1109/TDSC.2013.33
Saravanan, K., & Purusothaman, T. (2012). Efficient star topology based multicast key management algorithm. Journal of Computer Science, 8(6), 951-956 https://doi.org/10.3844/jcssp.2012.951.956
Saxena, N., & Yi, J. H. (2009). Noninteractive self-certification for long-lived mobile ad hoc networks. IEEE transactions on information forensics and security, 4(4), 946-955. https://doi.org/10.1109/TIFS.2009.2031946.
Saxena, N., Tsudik, G., & Yi, J. H. (2008). Efficient node admission and certificateless secure communication in short-lived MANETs. IEEE Transactions on Parallel and Distributed Systems, 20(2), 158-170. https://doi.org/10.1109/TPDS.2008.77.
Sepulcre, M., Gozalvez, J., & Lucas-Estañ, M. C. (2019). Power and packet rate control for vehicular networks in multi-application scenarios. IEEE Transactions on Vehicular Technology, 68(9), 9029-9037.
Srilakshmi, U., Veeraiah, N., Alotaibi, Y., Alghamdi, S. A., Khalaf, O. I., & Subbayamma, B. V. (2021). An improved hybrid secure multipath routing protocol for MANET. IEEE Access, 9, 163043-163053 https://doi.org/10.1109/ACCESS.2021.3133882.
Subramaniyan, S., Johnson, W., & Subramaniyan, K. (2014). A distributed framework for detecting selfish nodes in MANET using Record-and Trust-Based Detection (RTBD) technique. EURASIP Journal on Wireless Communications and Networking, 2014(1), 1-10 https://doi.org/10.1186/1687-1499-2014-205.
Veeraiah, N., Khalaf, O. I., Prasad, C. V. P. R., Alotaibi, Y., Alsufyani, A., Alghamdi, S. A., & Alsufyani, N. (2021). Trust aware secure energy efficient hybrid protocol for manet. IEEE Access, 9, 120996-121005. https://doi.org/10.1109/ACCESS.2021.3108807.
Vijayakumar, P., Azees, M., Kannan, A., & Deborah, L. J. (2016). Dual authentication and key management techniques for secure data transmission in vehicular ad hoc networks. IEEE Transactions on Intelligent Transportation Systems, 17(4), 1015-1028 https://doi.org/10.1109/TITS.2015.2492981.
Vijayakumar, P., Bose, S., Kannan, A., & Jegatha Deborah, L. (2013). Computation and communication efficient key distribution protocol for secure multicast communication. KSII Transactions on Internet and Information Systems (TIIS), 7(4), 878-894 https://doi.org/10.3837/tiis.2013.04.016.
Wei, Z., Tang, H., Yu, F. R., Wang, M., & Mason, P. (2014). Security enhancements for mobile ad hoc networks with trust management using uncertain reasoning. IEEE Transactions on Vehicular Technology, 63(9), 4647-4658.
Wu, W. C., & Liaw, H. T. (2015). A study on high secure and efficient MANET routing scheme. Journal of Sensors, 2015. https://doi.org/10.1155/2015/365863.
Yadava, M., Pandey, A. S., & Singh, K. (2021). Secure and efficient wireless multicast communication using trust-based key management. Journal of Discrete Mathematical Sciences and Cryptography, 24(3), 711-727.
Zhang, R., Han, W., Zhang, L., Wang, L., & Meng, X. (2023). Provably Secure Receiver-Unrestricted Group Key Management Scheme for Mobile Ad Hoc Networks. Sensors, 23(9), 4198.
Zhang, Y., & Lee, W. (2000, August). Intrusion detection in wireless ad-hoc networks. In Proceedings of the 6th annual international conference on Mobile computing and networking (pp. 275-283). https://doi.org/10.1145/345910.345958
Zhou, J., & Ou, Y. H. (2009). Key tree and Chinese remainder theorem based group key distribution scheme. In Algorithms and Architectures for Parallel Processing: 9th International Conference, ICA3PP 2009, Taipei, Taiwan, June 8-11, 2009. Proceedings 9 (pp. 254-265). Springer Berlin Heidelberg. https://doi.org/10.1007/978-3-642-03095-6_26
Zhao, S., Aggarwal, A., Frost, R., & Bai, X. (2011). A survey of applications of identity-based cryptography in mobile ad-hoc networks. IEEE Communications surveys & tutorials, 14(2), 380-400.
Zheng, X., Huang, C. T., & Matthews, M. (2007, March). Chinese remainder theorem based group key management. In Proceedings of the 45th annual southeast regional conference (pp. 266-271) https://doi.org/10.1145/1233341.1233389

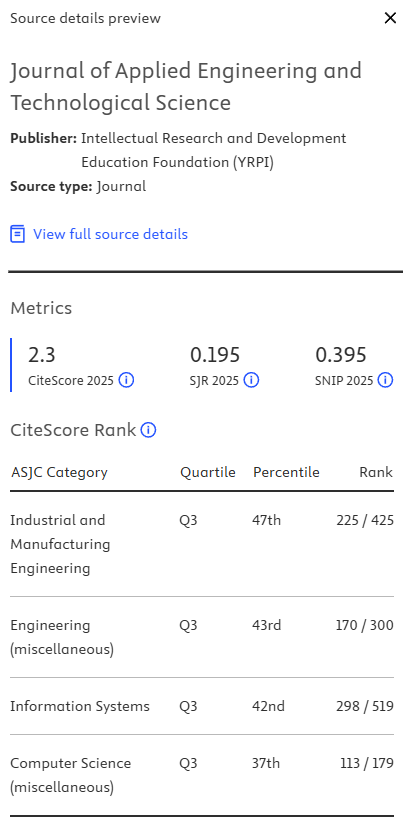


 CITEDNESS IN SCOPUS
CITEDNESS IN SCOPUS CITEDNESS IN WOS
CITEDNESS IN WOS








